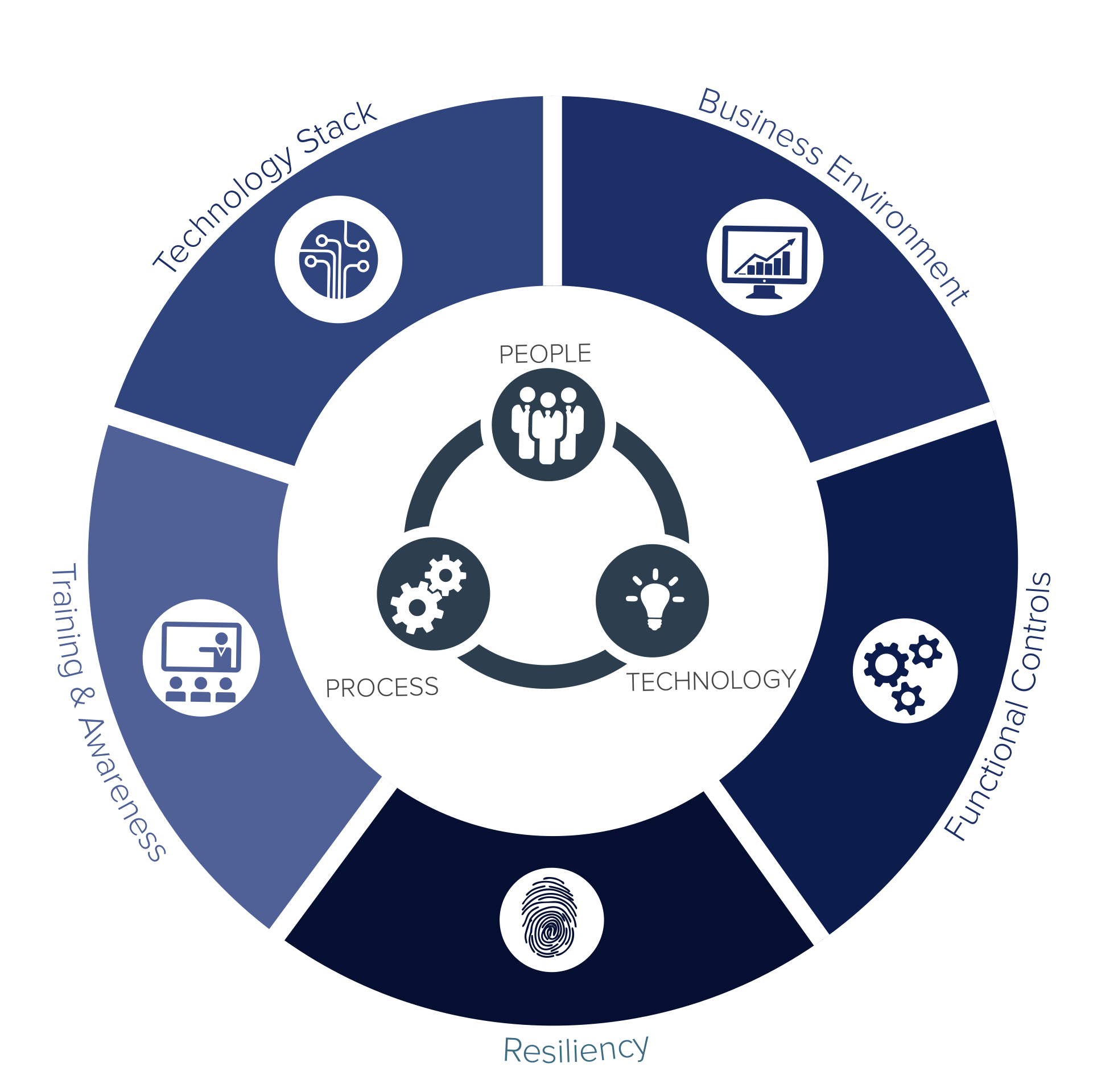
Diagnose your digital stack against best in class cyber attacks assessing your people, process and technology,
to get a quantitative analysis of the risk your business is presently sitting on,
along with an actionable roadmap to mitigate the identified gaps.

Predefined Maturity Levels
Controls across People, Process & Technology
Compliance Frameworks Included within Scope
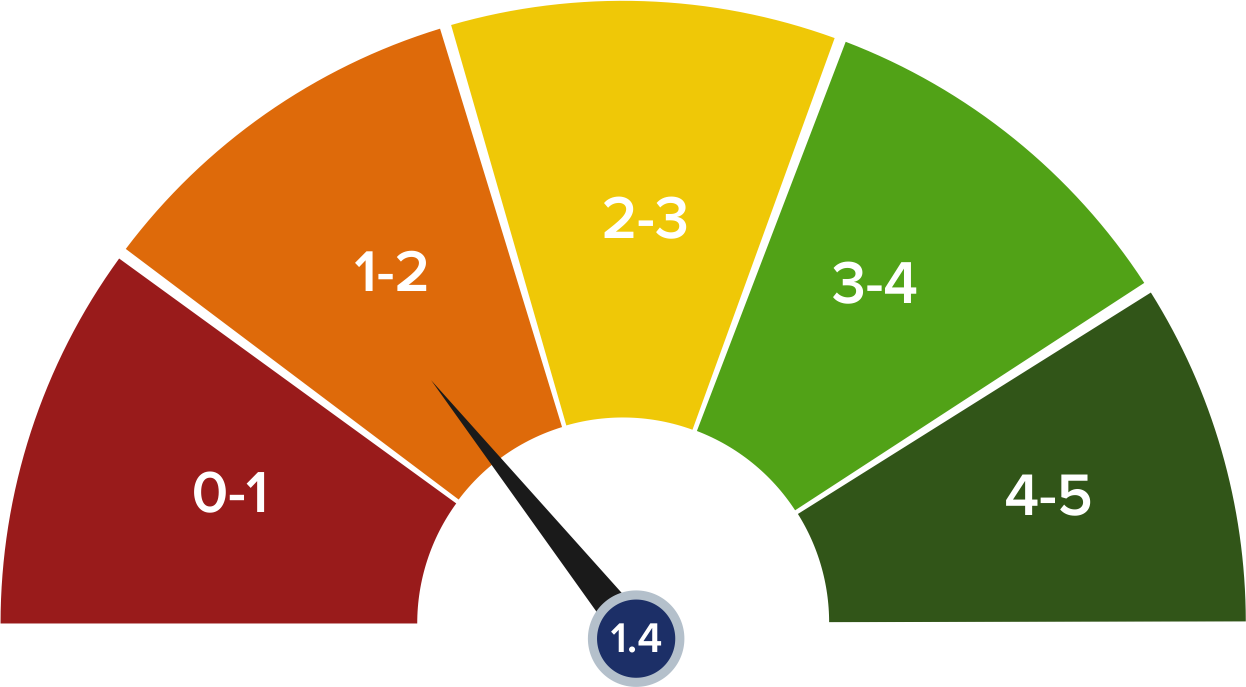
We provide you a scorecard of your overall IT Security Maturity after gathering information and assessing your people, process & technology stack against over 400 controls of ours so that you get to see on a quantised manner the risk you are sitting on, such that you can plan the future action plan accordingly.
Our final report will not only point at the identified gaps in the organisation but also provide a point by point analysis of actionable recommendations categorised as short term and long term along with Free of Cost and Commercial fixes to enhance the maturity of the organisation.

We will not only provide to you a roadmap but will also help you implement the low hanging quick fixes that can enhance your IT Security Maturity within 90 days.
Alras Information Technology L.L.C Regus Business Center Upper Mezzanine Floor, Hormuz Grand Hotel Al Matar Street, Muscat P.O Box 395 PC 118 Sultanate of Oman
+968-90155190
info@alras.om